Operations | Monitoring | ITSM | DevOps | Cloud
7 Ways UEM Enhances Your Security
Introduction Many things blur the line between endpoint management and security. Examples? Managing an endpoint. Configuring it. Performing application and software management. And patching the endpoint. The fact is, managing and securing a device is so interrelated that it makes sense for these two functions to come together in a single platform that can accomplish these, and other tasks needed in your IT organization. Here are the seven ways Unified Endpoint Management (UEM) can support security.
HLS Monitoring with Catchpoint
In this tech tip, we are focusing on HLS (HTTP Live Streaming), a streaming protocol released by Apple in 2009. HTTP Live Streaming is widely used and it isn’t just limited to streaming services like Netflix or YouTube – it’s an important protocol for all content providers and CDNs. You’ll basically find HLS anywhere people want on-demand streaming.
Icinga for Windows - Hyper-V and Cluster Plugins Preview
Today we finally have great news to share for everyone using Icinga to monitor Hyper-V and Windows Cluster environments. For quite some time we’ve been working on multiple new plugins to provide better monitoring option for Hyper-V and Windows Cluster. The new plugins are based on our PowerShell framework provided by Icinga for Windows. For the new plugins we decided to provide a preview first, in favour of a final release.
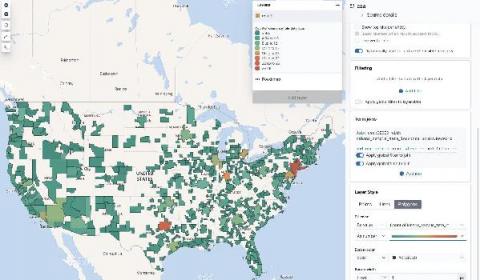
How to map custom boundaries in Kibana with reverse geocoding
Want to create a map of where your users are? With the GeoIP processor, you can easily attach the location of your users to your user metrics. Right out of the box, Kibana can map this traffic immediately by country or country subdivision: Plus, the new User Experience app for Elastic APM automatically creates maps based on monitoring data: But what if you want to take this one step further and create maps with different regions?
Why AlertOps is the best PagerDuty alternative
4 Essential Types of MSP Tools (in 2021)
Why Are Some Engineers Missing The Point of Serverless?
Recently, I saw a video from a really great developer and YouTuber, Ben Awad, where he discussed Serverless not make any sense. Even though I really enjoyed the video, I am not sure if the author’s points about serverless are entirely valid, and I want to discuss them in this article.
What's Next for Department of Defense Digital Modernization?
As the Trump Administration comes to a close, there is no better time than the present to reexamine the Department of Defense Digital Modernization Strategy and its potential sustainment beyond January 2021.
Macros, We Don't Need No Stinking Macros! - Featuring the New Microsoft O365 Email Add-On
Recently, I’ve been on a mission building a new Microsoft Office 365 Email Add-on for Splunk. This has been built for use with Splunk Enterprise, while making sure that it properly supports Splunk’s Common Information Model (CIM). CIM is paramount when wanting data to play nicely with Splunk Enterprise Security.