Hurricane Helene Devastates Network Connectivity in Parts of the South
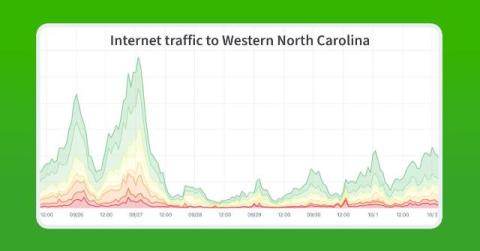
In this post, we dig into the impacts from Hurricane Helene which came ashore late last month wreaking destruction and severe flooding in the Southeastern United States. Using Kentik’s traffic data as well as Georgia Tech’s IODA, we detail the impacts in three of the hardest-hit states: Georgia, South Carolina, and North Carolina.