Operations | Monitoring | ITSM | DevOps | Cloud
Latest News
Keep my data private
How to allow customers to easily request data privacy under the California Consumer Privacy Act Julie, who recently took up baking cupcakes as a hobby, is furious—and not about her culinary skills. She hadn’t realized how much of her personal information the company from which she bought her supplies had harvested and sold, without her express permission.
How CFEngine stays ahead of the pack
CFEngine was the first Configuration Management solution on the market, and while we have made many and significant changes and improvements to CFEngine in that time, we stay true to the principles that make it such a great product and technology. There are many things that have changed in the market, not at least the competitive situation, we believe that fundamentally many of the challenges stay the same. It then follows that good architecture should not be sacrificed for short term hype.
Attack of the mutant tags!Or why tag mutability is a real security threat
Tag mutability can introduce multiple functional and security issues. In container land, tags are a volatile reference to a concrete image version in a specific point in time. Tags can change unexpectedly, and at any moment. In this article, we’ll learn how we can prevent them.
Three Ways Federal Agencies Can Manage and Secure Their Hybrid Data Centers
Machine learning in cybersecurity: Training supervised models to detect DGA activity
How annoying is it when you get a telemarketing call from a random phone number? Even if you block it, it won’t make a difference because the next one will be from a brand new number. Cyber attackers employ the same dirty tricks. Using domain generated algorithms (DGAs), malware creators change the source of their command and control infrastructure, evading detection and frustrating security analysts trying to block their activity.
Countdown to CCPA enforceability
The California Consumer Privacy Act (CCPA) is a new act that strengthens and unifies data protection for consumers by giving California residents more control over their personal information. This regulates not only how it is collected and used, but also, how it is sold by companies. The CCPA went into effect January 1, and enforcement will begin July 1.
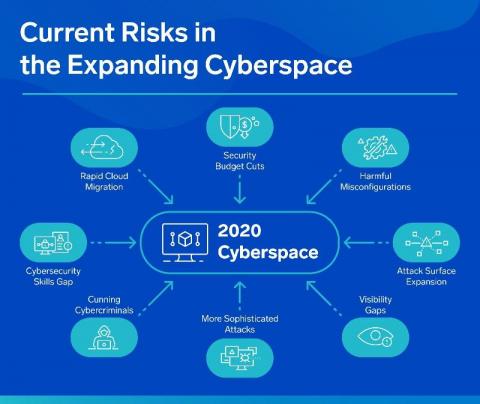
Prevent and Detect Threats Across Multi-Cloud Environments
The cloud has become ubiquitous in all we do, and the line between the perimeter and the cloud continues to shrink as most enterprise organizations are looking to shift their cloud strategy to a multi-cloud approach. Moving to the cloud comes with plenty of benefits like performance optimization, improved reliability and overall cost savings, but cloud adoption is not without its risks and challenges.
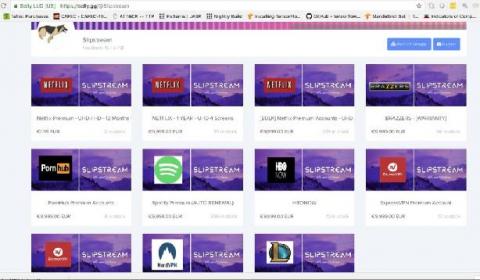
The value of a stolen account. A look at credential stuffing attacks.
Azure you shot an ARO through our hearts... Confidently observe and secure Azure Red Hat OpenShift with Sysdig and Arctiq
It has arrived! Azure Red Hat OpenShift 4 is here and generally available; now, how do you add even more granular security and faster time to repair (MTTR) for your teams? Sysdig, that’s how!