Operations | Monitoring | ITSM | DevOps | Cloud
The latest News and Information on Cloud monitoring, security and related technologies.
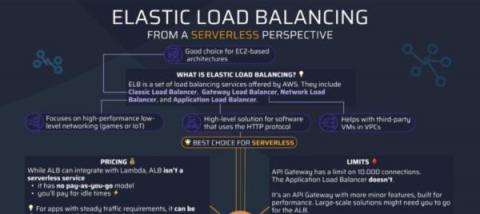
[Infographic] AWS Elastic Load Balancing from a Serverless perspective
Load balancing is a significant part of every internet-facing software, and with Elastic Load Balancing (ELB), AWS offers a set of load balancers for every use case. Since our latest update, Dashbird also gives you insights into these ELB services; let’s look at them and see how they can be used in a serverless environment.
How to Implement FinOps Successfully - Episode 5 / Operate Phase
This is the fifth and final part of this FinOps series, The Operate Phase. If you have missed any of my previous blogs, here is a list of posts in the series: Note: I am ex-AWS, so you will notice a lot more focus on AWS tools and services as examples here, however we are cloud agnostic and all cloud providers have similar services and tools.
Kubernetes: Visualizing Performance & Risk
Top 10 Monitoring Features for Multi-Tenant Managed Service Providers (MSPs)
eG Innovations works with Managed Service Providers (MSPs) across the world, who use eG Enterprise to deliver value-added services to improve their customers’ resilience and business outcomes. Many of these service providers choose eG Enterprise for its secure and granular role-based multi-tenancy support. The service provider does not have to configure and maintain one instance of eG Enterprise for each customer.
Amazon S3 Cost Optimization Best Practices
Amazon Simple Storage Service (S3) is an essential cornerstone of AWS and among its most popular service offerings. S3 allows tenants to store, secure, and retrieve data from S3 buckets on demand. It is widely used for its high availability, scalability, and performance. It supports six storage classes and several use cases, including website hosting, backups, application data storage, and data lake storage. There are two primary components of Amazon S3: Buckets and Objects.
Upsun Announces Microsoft Azure Support for the Australian Market
Elevate AWS threat detection with Stratus Red Team
A core challenge for threat detection engineering is reproducing common attacker behavior. Several open source and commercial projects exist for traditional endpoint and on-premise security, but there is a clear need for a cloud-native tool built with cloud providers and infrastructure in mind. To meet this growing demand, we’re happy to announce Stratus Red Team, an open source project created to emulate common attack techniques directly in your cloud environment.