Operations | Monitoring | ITSM | DevOps | Cloud
4 lessons from the telecom industry
The pandemic has accelerated innovation as more companies scramble to be future-ready, flexible, and adaptable. Having quickly responded to a crisis and executed a planned digital transformation at UK telecommunications giant BT, I want to share lessons we learned to help other companies transition smoothly to a more digital future. Customers at the core The telecom industry has been changing rapidly over the past few years. The lines between work and play are becoming increasingly blurred.
Performance Monitoring for Android Applications
Android is arguably the most ubiquitous operating system in the world. Whether it’s a tablet, phone, folding phone, computer, TV, or IoT device, chances are you’ve interacted with Android OS. And to help developers get full visibility into how their customers experience Android’s myriad applications, we’re extending Performance to Android.
Logz.io Infrastructure Monitoring: Building Visualizations in Dashboards
In a previous post I explained how to send metrics to Logz.io Infrastructure monitoring with Prometheus—now let’s analyze them by building Prometheus dashboards and visualizations in our metrics UI! Once you’ve started to send metric data to Logz.io, how do you visualize and interpret that data so that it’s useful for you? Logz.io Infrastructure Monitoring provides powerful querying and visualization of your data.
Monitoring Windows Event Logs - Getting Started
Windows event logs are important for security, troubleshooting, and compliance. When you analyze your logs, you can monitor and report on file access, network connections, unauthorized activity, error messages, and unusual network and system behavior. However, Windows servers produce tens of thousands of log entries every day.
The Relationship Between Observability vs. Monitoring
Monitoring has always been a crucial operation in a software development cycle. This is mainly because of the complexity of industry-level IT and consumer-facing product development. Additionally, there is an ever-growing demand for rapid upgrades in products. To meet these requirements, streamlined performance and stability have become more important than ever; and without effective monitoring practices, they appear difficult to achieve.
How to Understand Log Levels
More than once, I’ve heard experienced software developers say that there are only two reasons to log: either you log Information or you log an Error. The implication here is that either you want to record something that happened or you want to be able to react to something that went wrong. In this article, we’ll take a closer look at logging and explore the fact that log levels are more than just black or red rows in your main logging system.
Is Your Home Built to Last? Investing in Cloud-Based ITSM for a More Secure Tomorrow
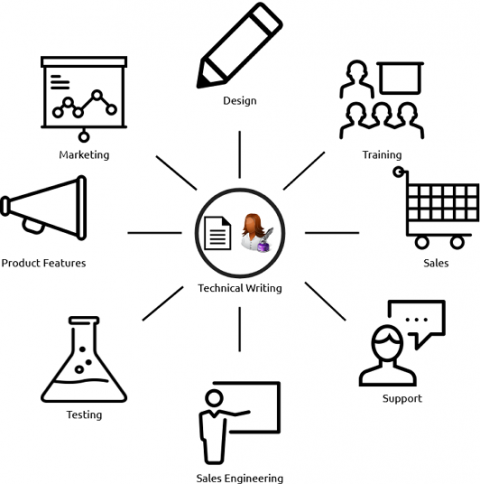
Effective Technical Writing Is Essential for Your Organization's Success
The DevSecOps Cultural Transformation
Let’s take a moment and think about security in your organization. Security is often separate from other engineering teams such as development, operations, networking, IT, and so forth. If you narrow down your focus to specifically releasing new software or features and functions in existing software, you’ll find that while development and operations are working together very quickly and efficiently, they’re still vaulting these functions and features over to security.