Operations | Monitoring | ITSM | DevOps | Cloud
SAN Performance Monitoring
A Storage Area Network (SAN) is a specialized, high-speed network that provides block-level network access to storage. SANs are typically composed of hosts, switches, storage elements, and storage devices that are interconnected using a variety of technologies, topologies, and protocols. Each computer on the network can access storage on the SAN as if they are local disks connected directly to the computer.
Comparison N-Able vs Kaseya vs Pandora FMS: Fight !!!
Lemons, oranges, grapefruits, limes… We know that they are not the same, but if necessary, you can make juice with all of them. And yes, we can and we will. We are in summer and it makes you want to make a good cocktail, doesn’t it? Today, in PFMS blog, we are going to analyze the commonalities of N-Able (Solarwinds MSP), Kaseya and Pandora FMS. Also their -remarkable- differences of course.
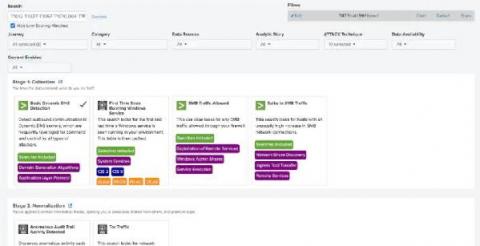
Get Started with Splunk for Security: Splunk Security Essentials
Continuing to ride the waves of Summer of Security and the launch of Splunk Security Cloud, Splunk Security Essentials is now part of the Splunk security portfolio and fully supported with an active Splunk Cloud or Splunk Enterprise license. No matter how you choose to deploy Splunk, you can apply prescriptive guidance and deploy pre-built detections from Splunk Security Essentials to Splunk Enterprise, Splunk Cloud Platform, Splunk SIEM and Splunk SOAR solutions.
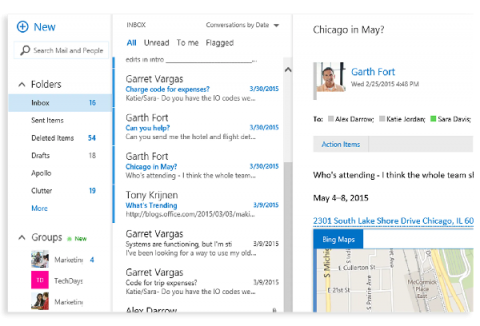
Analyzing Office 365 GCC Data With Sumo Logic
Top 5 Web Application Monitoring Tools You Should Know
Web application monitoring tools can keep your business afloat. Period. Imagine this. You’re about to run a crucial end-of-season sale on your website. You’ve sent your emails, run social media campaigns, paid for advertisements, and stocked up your inventory; you are all set to let the cash register ring. However, on D-day, your website goes down. It’s unable to handle the incoming traffic or is simply down because of technical glitches.
A Step By Step Guide to Tomcat Performance Monitoring
Application server monitoring metrics and runtime characteristics are essential for the applications running on each server. Additionally, monitoring prevents or resolves potential issues in a timely manner. As far as Java applications go, Apache Tomcat is one of the most commonly used servers. Tomcat performance monitoring can be done with JMX beans or a monitoring tool such as MoSKito or JavaMelody.
The New Normal for Hybrid IT Solutions
OnPage Corporation Celebrates 10 Years of Growth and Innovation
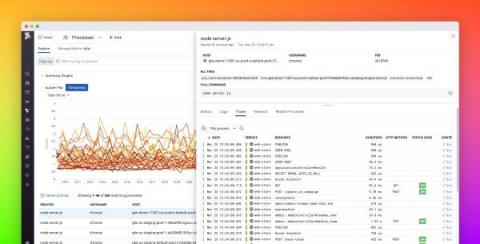
Troubleshoot faster with process-level app and network data
When responding to an incident, you need to quickly find the scope of the issue so you know which teams to notify and which parts of your system to investigate next—before your end users are affected. But as multiple processes use resources on each of your hosts, and interact in unexpected ways, it can be difficult to know exactly what is causing an issue—especially if those processes are running off-the-shelf software.