Operations | Monitoring | ITSM | DevOps | Cloud
The latest News and Information on CyberSecurity for Applications, Services and Infrastructure, and related technologies.
Understanding Zero-Day Vulnerabilities in Software Supply Chain
Kubernetes Security Challenges with Armo - Insights from KubeCon NA 2023 - Civo TV
Electronic Signature - How It Works
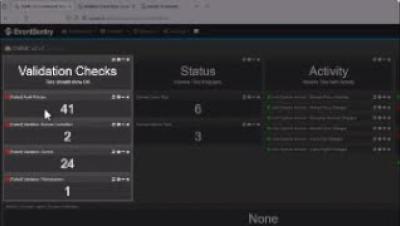
CMMC v2 Compliance with EventSentry
Out-of-band communication: Maintaining business continuity
Today, most organizations rely on several different secure communication mediums — like email, real-time chat, video calls, and SMS — to transmit information, collaborate, and keep teams aligned. While modern communication tools help teams stay connected, the digital landscape is not without its challenges. For most organizations, it’s only a matter of time before network disruptions, security breaches, and system failures impact main lines of communication.
Analytics Plus webinar: Catch critical signs of vulnerable security protocols
Analytics Plus webinar: How to make the help desk your first line of cyberdefense
Warning Signs of Weak Cyber Security
Succeeding with Backstage 3: Improving Adoption
This third installment of the “Succeeding with Backstage” series explores how you can improve the adoption of Backstage within your organization. The previous two parts dealt with customizing the look and feel of Backstage and creating and maintaining custom plugins.