Operations | Monitoring | ITSM | DevOps | Cloud
The latest News and Information on CyberSecurity for Applications, Services and Infrastructure, and related technologies.
IT vs Security - When Hackers Patch for Profit | Ep.31 Security Insights Podcasts
Micro Product Demo: Ivanti Neurons for Patch Management
Practical Demo: Protect all endpoints with secure UEM countermeasures
Public Web Data: Main Reasons to Leverage Data in Your Business Operations
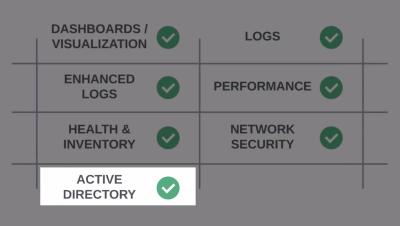
EventSentry in under 5 minutes
N-able Empowers MSPs with Enterprise-Grade Security Solutions
Everything you need to know about data sovereignty
In today’s digital age, the most effective organizations are using data to fuel innovation and accelerate business strategies. Data continues to be at the heart of business growth. Organizations increasingly rely on technology to manage and store their data. Questions about ownership, control, and security have emerged — leading to the rise of a concept known as data sovereignty. In this post we’ll explore.
6 Ways Cloud-based Computerized Accounting Systems Can Help Small Businesses
(Crowd)Strike While the Data Is Hot: Getting Started with CrowdStream, Powered by Cribl
In today’s landscape, what’s considered security data has expanded to encompass more diverse data types like network data, behavioral analytics, and application metrics. These sources are now essential for a comprehensive security strategy, and visibility into all that data makes proactive threat detection possible. That said, organizations often struggle to process data from various vendors and merge telemetry sets to gain a complete view of their environments.