Operations | Monitoring | ITSM | DevOps | Cloud
The latest News and Information on CyberSecurity for Applications, Services and Infrastructure, and related technologies.
Detect suspicious activity in GCP using audit logs
GCP audit logs are a powerful tool that track everything happening in your cloud infrastructure. By analyzing them, you can detect and react to threats. Modern cloud applications are not just virtual machines, containers, binaries, and data. When you migrated to the cloud, you accelerated the development of your apps and increased operational efficiency. But you also started using new assets in the cloud that need securing.
Cloud lateral movement: Breaking in through a vulnerable container
Lateral movement is a growing concern with cloud security. That is, once a piece of your cloud infrastructure is compromised, how far can an attacker reach? What often happens in famous attacks to Cloud environments is a vulnerable application that is publicly available can serve as an entry point. From there, attackers can try to move inside the cloud environment, trying to exfiltrate sensitive data or use the account for their own purpose, like crypto mining.
AWS CIS: Manage cloud security posture on AWS infrastructure
Implementing the AWS Foundations CIS Benchmarks will help you improve your cloud security posture in your AWS infrastructure. What entry points can attackers use to compromise your cloud infrastructure? Do all your users have multi-factor authentication setup? Are they using it? Are you providing more permissions that needed? Those are some questions this benchmark will help you answer. Keep reading for an overview on AWS CIS Benchmarks and tips to implement it.
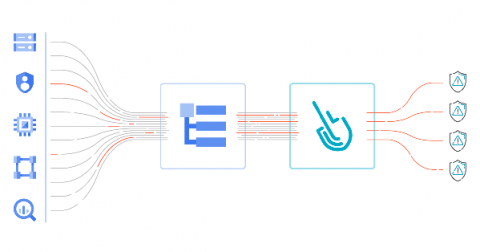
Unified threat detection for AWS cloud and containers
Implementing effective threat detection for AWS requires visibility into all of your cloud services and containers. An application is composed of a number of elements: hosts, virtual machines, containers, clusters, stored information, and input/output data streams. When you add configuration and user management to the mix, it’s clear that there is a lot to secure!
Credential management best practices for business process automations
Using Policy Analyzer to develop and debug CFEngine policy
I have a setup at home where I keep a local git server running on a Raspberry Pi 3 which contains personal/work journal, dotfiles and a personal policy repository. It was set up manually so before adding a new git repository for a family password store I set about retrofiting the configuration in CFEngine. The goal in this blog is to ensure that what I have already is managed by CFEngine and that what I want to add, /srv/git/passwords.git, is created.
Automated Clean-up of HAFNIUM Shells and Processes with Splunk Phantom
If you haven’t been living under a rock for the past few weeks, you've probably come across the recent Microsoft Exchange Server vulnerabilities and its associated exploits.Stop!!! The first thing you should do is to go and patch any Exchange servers you may be running, then you can come back and finish reading this blog. Microsoft's blog provides links to various tools to help in this regard.