Operations | Monitoring | ITSM | DevOps | Cloud
The latest News and Information on CyberSecurity for Applications, Services and Infrastructure, and related technologies.
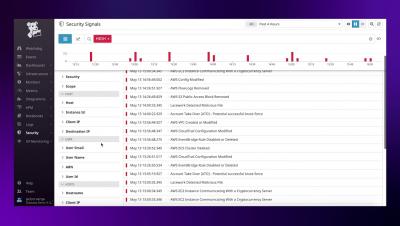
Datadog Security Monitoring Overview
Datadog Security Monitoring allows you to detect threats in real time and investigate security signals across your infrastructure, applications, and network. This video shows you the capabilities and how you can be up and running in just a few minutes.
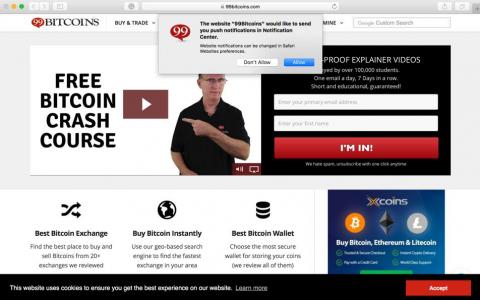
Spam In the Browser
A new kind of spam is being observed in the field that uses the browser notification feature to trick users into subscribing to sites that will in turn bombard users with notifications usually related to click or add profit schemes. Subscription notification request seen below: Browser notification subscription requests are a legitimate feature that allows visitors of a site to be notified when there is new content available. It saves users the need to constantly refresh or keep open browser tabs.
Ubuntu 20.04 LTS to enforce stronger TLS v1.2 encryption by default
In Ubuntu 20.04 LTS, the OpenSSL 1.1.1f library has been modified to use Security Level 2 by default (previous versions of Ubuntu use Security Level 1). Security Level 2 guarantees that protocols, key exchange mechanisms, cipher suites, signature algorithms, certificates and key sizes provide a minimum of 112 bits of message secrecy. In practice, it means that RSA keys are required to be at least 2048 bits long and ECC keys at least 224 bits using the SHA256 certificate signature algorithm.
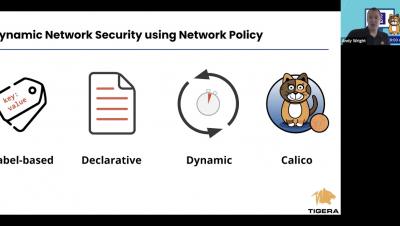
Network Security for D2iQ Konvoy
By default, pods are non-isolated; they accept traffic from any source. The D2iQ Konvoy solution to this security concern is Network Security Policy that lets developers control network access to their services. D2iQ Konvoy comes preconfigured with Network Security Policy using Project Calico which can be used to secure your clusters. This class will describe a few use cases for network policy and a live demo implementing each use case.
Getting DevSecOps Right in Financial Services
Join this webinar to learn best practices and patterns used by some of the largest FinServ enterprises in the world to accelerate software releases while mitigating risk. Discover how to enable security, compliance, and auditability as an integral part of your DevOps processes, at scale.
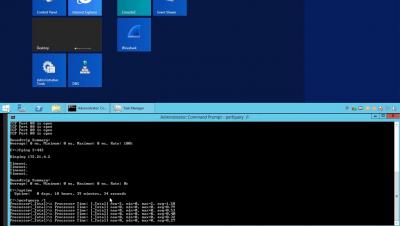
SysAdminTools vs No Tools
Shows the most popular applications from the tool set in action. The split screen video illustrates how much more easier common tasks are with the SysAdmin Tools!
9 Low-Cost or Free Cybersecurity Training Resources
When it comes to cybersecurity, the landscape is constantly changing: the number of cyberattacks is always on the rise, the attacks themselves are becoming more sophisticated, and there’s a serious skills shortage in the industry. There’s a lot to learn about cybersecurity if you want to keep up and keep your users protected.