Operations | Monitoring | ITSM | DevOps | Cloud
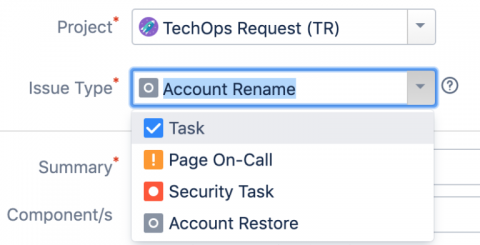
Using Lambda and JIRA to Handle DevOps Tasks
“Value ++” One of our engineers on the TechOps team coined that term. It references the shorthand operator for “increment” in various coding languages. It also is a motto for what we should be doing as a team… always adding value.
IT analytics in 90 seconds: Ensure customer retention through first call resolutions
Surface Kubernetes Errors with Sentry
Kubernetes, like a lot of other tools, can be noisy. Errors and warnings often go completely unnoticed in the event stream. Or sometimes they are noticed, but are hard to understand in the context of what else is happening in the cluster. Sentry, unlike a lot of other tools, works to eliminate that noise as much as possible, including Kubernetes-related noise.
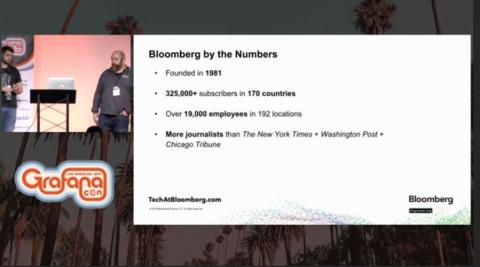
How Bloomberg Tracks Hundreds of Billions of Data Points Daily with MetricTank and Grafana
Bloomberg is best known as a media company with its news destination site, its award-winning magazine Bloomberg Businessweek, and its daily 24-7 social media program, Tic Toc, on Twitter. But the main product for the 38-year-old company is actually Bloomberg Terminal, a software system that aggregates real-time market data and delivers financial news to more than 325,000 subscribers around the world.
Using GitLab Auto DevOps with Kubernetes Through Rancher's Authorized Cluster Endpoint
In this post, we will walk through how to connect GitLab’s Auto DevOps feature with a Rancher-managed Kubernetes cluster, making use of a feature introduced in Rancher v2.2.0 called Authorized Cluster Endpoint. Readers can expect to walk away with an understanding of how GitLab integrates with Kubernetes and how Rancher simplifies this workflow with Authorized Cluster Endpoint.
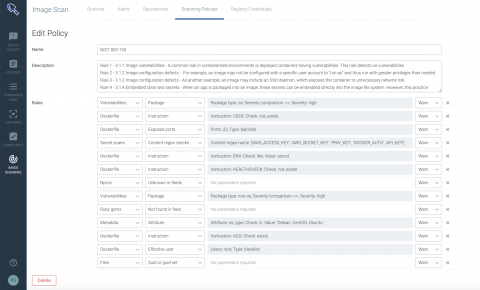
Cloud Native visibility and security with Sysdig Platform
NIST SP 800-190 application container security with Sysdig Secure
In September 2017, the National Institute of Standards and Technology (NIST) released Special Publication (SP) 800-190, Application Container Security Guide. NIST SP 800-190 explains the security concerns associated with container technologies and recommendations for the image details and container runtime security. It provides prescriptive details for various sections including image, registry, orchestrator, container and host OS countermeasures.
NYC Kafka Meetup: How To Rewind The New York Times Homepage and Capacity Planning at Datadog
Releasing Icinga Reporting for Early Adopters
We’re happy to announce that we released an early version of Icinga Reporting today! With this release we create the foundation for an overall reporting functionality for Icinga by introducing a new way to work with collected data. At the same time we are also publishing the first use case of Icinga Reporting which enables you to calculate, display and export SLA reports for your hosts and services.