What's All the Fuss About Business Continuity Planning
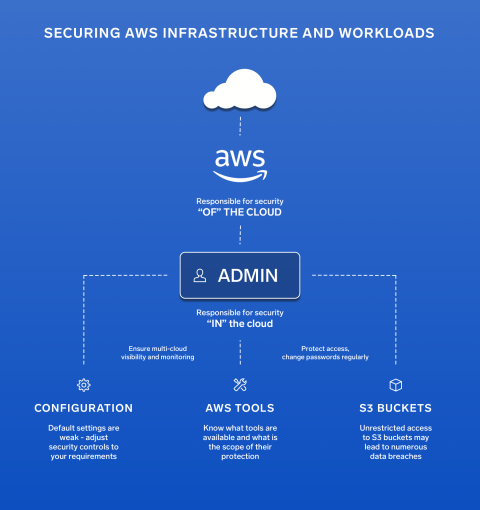
Digital transformation has created more gateways for vulnerability and risk. So in addition to natural disasters that can impact a business, organizations are faced with cyberattacks that can truly cripple their business. A solid business continuity plan makes sure that your company is ready for whatever may come its way, be it fire, flood, critical technical failure, or a cyberattack.