Operations | Monitoring | ITSM | DevOps | Cloud
The latest News and Information on DevOps, CI/CD, Automation and related technologies.
Announcing support for Windows containers on AWS Fargate
AWS Fargate is a serverless compute engine that allows you to deploy containerized applications with services such as Amazon ECS without needing to manage the underlying virtual machines. Deploying with Fargate removes operational overhead and lowers costs by enabling your infrastructure to dynamically scale to meet demand. We are proud to partner with AWS for its launch of support for AWS Fargate on Windows containers.
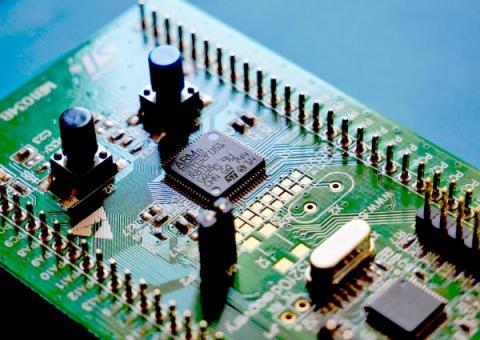
ARM vs Intel: What Are They? What is the Difference Between Them?
Most computing devices today are likely to have an Intel processor, or an ARM (Advanced RISC Machine) processor, such as the CPU in your smartphone or tablet. Both chip architectures are optimised for low-power operation in order to provide mobile devices with the long battery life they require. However, they reflect different mindsets from a technical standpoint.
Kubernetes Master Class Security & Observability feat. Tigera
Kubernetes Master Class Managing Cluster Security at Scale
6 Steps SREs Should Take to Prepare for Black Friday and Cyber Monday 2021
Six tips on how Site Reliability Engineers (SREs) can prepare for the reliability challenges of Black Friday and Cyber Monday 2021
10 practices that are changing in software today with Alex Williams
How to rename an API Connection thru the Azure Portal
Linux Mint vs Ubuntu: Who will win?
Linux is an open-sourced operating system for computers, smartphones, servers, mainframes, and embedded devices. The main advantage of Linux over other operating systems is that Linux is an open-source operating system, which means that you can view, edit, customize, enhance, and share the code with anyone. The release of Linux garnered a huge community of contributors that created a variety of features and distributions for users at no added cost.
What is embedded Linux? Part I
“Hello everybody out there using minix – I’m doing a (free) operating system (just a hobby, won’t be big and professional like gnu) for 386(486) AT clones. The above is an excerpt from Linus Torvalds’ original announcement of what came to be known worldwide as the Linux operating system (OS), dated August 1991. In hindsight, it is inconceivably modest now that we are in a much better position to appreciate the full revolutionary extent of his post.