Operations | Monitoring | ITSM | DevOps | Cloud
To be or not to be? To do - or not to do - an ELP?
Before I start my ramble here, let me tell you something... the day I learned how to construct a manual Effective License Position (ELP) in Excel my life gained a new purpose, and it became the biggest hobby, sport and passion ever! Those who have done manual ELPs in Excel will know that magic feeling! First, it’s hard as you scramble for the data and licensing knowledge, but if you’re lucky enough and at least get some vendor report or purchase summary, it's a good starting point...
Debugging Filters and Apply Rules using the Script Debugger
Have you ever been in a situation where something in your Icinga configuration did not work as expected and you ended up doing small changes and reloading Icinga over and over again? This can be especially tricky with apply rules and filters if they don’t match the objects you hope for. This post will show you how you can use the Icinga Script Debugger in this situation to get an interactive console in the context where the apply rule or filter is evaluated.
MITRE Engenuity ATT&CK Round 3: Carbanak + FIN7 vs. the free and open capabilities in Elastic Security
Whether this is the third time you are looking at the MITRE Engenuity ATT&CK® evaluation results or your first, you may be asking yourself: what was unique about this year’s evaluation? Well, let’s first start with: who is MITRE Engenuity? They are a tech foundation that collaborates with the private sector on many initiatives — most notably cybersecurity — and in recent years have become synonymous with cyber threat evaluations.
Getting started with free and open Elastic Observability
Unify and contextualize your logs, metrics, application trace data, and availability data behind a single pane of glass. Elastic Observability provides a unified view into the health and performance of your entire digital ecosystem. With easy ingest of multiple kinds of data via pre-built collectors for hundreds of data sources, Elastic Observability delivers seamless integration between the facets of observability.
The true cost of IT Ops, the added value of AIOps
Today’s IT landscape is complex, hybrid, and fast-moving, and the adoption of multi-cloud infrastructure, applications, and new digital transformation initiatives is accelerating. IT operations teams, playing a vital role in enabling the delivery of uninterrupted services and creating business value for enterprises, are finding they need to constantly grow their resources to manage all the moving pieces in their IT stack. This can get expensive … but how much are they spending?
A Day in the Life: James the IT Ops Guy Learns How to Connect All that Data
“Morning, mate,” I greeted Dinesh as he walked into the office. “Nice get up for the big day!” He was wearing a pressed shirt, rather than his usual hoodie. “Thought I’d make an effort, you know,” he grinned. We’d been planning intensely for this moment for the last week or so – our meeting with Charlie, the CIO, to present the results of our Moogsoft experiments and ask for permission to extend the rollout across the enterprise.
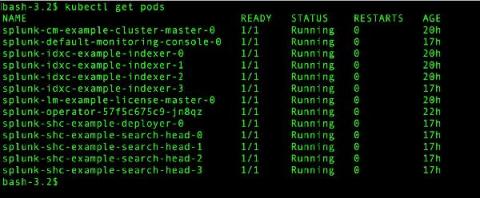
Going Live: Splunk Operator for Kubernetes 1.0.0
With everything going on in the world, it seems like a lifetime ago that we started talking about the Splunk Operator for Kubernetes, which enables customers to easily deploy, scale, and manage Splunk Enterprise on their choice of cloud environment. During that time, we’ve heard from an increasing number of on-premise and public cloud Bring-Your-Own-License Splunk customers that containerization and Kubernetes are an important part of their current and future deployment plans.
Monitoring Pulse Connect Secure With Splunk (CISA Emergency Directive 21-03)
To immediately see how to find potential vulnerabilities or exploits in your Pulse Connect Secure appliance, skip down to the "Identifying, Monitoring and Hunting with Splunk" section. Otherwise, read on for a quick breakdown of what happened, how to detect it, and MITRE ATT&CK mappings.