Operations | Monitoring | ITSM | DevOps | Cloud
The latest News and Information on IT Networks and related technologies.
Identifying Layer 7 application traffic to optimize WAN links
Network administrators around the globe are very concerned about the types of traffic in their networks. They want their critical business applications over the WAN to perform at their best. Non-critical apps, like social media apps, downgrade the performance of WAN links. Therefore, administrators should have the necessary controls to prioritize business applications on WAN links.
7 Ways to Prevent Network Security Breaches in the Workplace
Network security breaches are every business’s nightmare. A security breach could be anything from password attacks with further unauthorized system access to data leakage. Whether it is a small start-up or a large enterprise with millions of dollars in turnover, a single network security breach can be detrimental to the reputation of any company, not to mention the financial losses incurred. According to the 2021 Thales Data Threat Report, 45% of US companies suffered a data breach in 2020.
Monitor Calico with Datadog
Calico is a versatile networking and security solution that features a plugable dataplane architecture. It supports various technologies, including Iptables, eBPF, Host Network Service (HNS for Windows), and Vector Packet Processing (VPP) for containers, virtual machines, and bare-metal workloads. Users can employ Calico’s network security policies to restrict traffic to and from specific clusters handling customer data and to quickly block malicious IP addresses during external attacks.
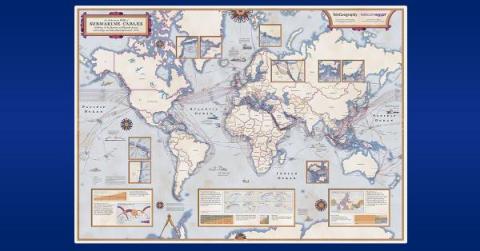
Diving Deep into Submarine Cables: The Undersea Lifelines of Internet Connectivity
Under the waves at the bottom of the Earth’s oceans are almost 1.5 million kilometers of submarine fiber optic cables. Going unnoticed by most everyone in the world, these cables underpin the entire global internet and our modern information age. In this post, Phil Gervasi explains the technology, politics, environmental impact, and economics of submarine telecommunications cables.
The 2023 Network IT Management Report Part 4: Solutions for End-Users
How to get the client IP in ASP.NET Core even behind a proxy
Part of implementing an error monitoring platform like elmah.io is dealing with the IP addresses of the clients generating errors. In this post, I'll show you parts of how we have implemented this in ASP.NET Core, to make sure that different hosting scenarios still produce the correct IP address. Let's jump right in. ASP.NET Core supports getting the client IP directly on the HttpContext object available throughout various places.
The Watchful Eye: Microsoft Network Monitoring for Microsoft Teams, Office 365 & Azure
Do you ever feel like someone's watching you? Well, when it comes to your company's network, you should hope so! With so many people relying on Microsoft Teams, Office 365, and Azure to keep their businesses running smoothly, it's more important than ever to keep a watchful eye on your network. But who has the time to monitor everything 24/7?
Digital Transformation Drives a New Cloud Era
To understand the cloud computing landscape today and what true digital transformation looks like, we should first understand how we got here.