Operations | Monitoring | ITSM | DevOps | Cloud
The latest News and Information on IT Networks and related technologies.
Why Broadcom IT Uses DX NetOps Instead of Other Industry Network Monitoring Solutions
Monitor Carbon Black Defense logs with Datadog
Creating security policies for the devices connected to your network is critical to ensuring that company data is safe. This is especially true as companies adopt a bring-your-own-device model and allow more personal phones, tablets, and laptops to connect to internal services. These devices, or endpoints, introduce unique vulnerabilities that can expose sensitive data if they are not monitored.
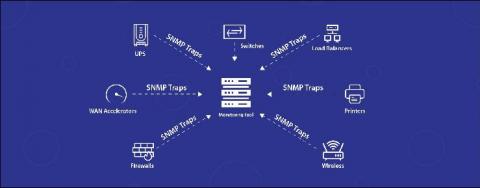
Complement your network monitoring with SNMP traps
Network device monitoring with Simple Network Management Protocol (SNMP) gives you complete visibility into the health and availability of your network devices. Monitoring tools conduct periodic checks to gather device status and performance metrics. The device's status is updated only when a check is initiated by the monitoring system in the defined time interval. Any fault that happens in between polls is only captured when the next check is initiated.
How to Configure Syslog on a Cisco Device
Meet Flowmon Packet Investigator
Everything You Need to Know about Kubernetes Services Networking in Your Rancher Cluster
As a leading, open-source multi-cluster orchestration platform, Rancher lets operations teams deploy, manage and secure enterprise Kubernetes. Rancher also gives users a set of CNI options to choose from, including open-source Project Calico.
How a Telecom Software Company Ensured Service Uptime with Network Monitoring
When you have millions of customers dependent on your connectivity & communication services performing with best possible efficiency, having network downtime because of any device failure is totally unacceptable. One of our customers is a proprietary global telecommunications vendor which designs, builds as well as manages data networks for telecoms all around the world.
Top 5 Network Performance Metrics | Obkio
Multus: how to escape the Kubernetes eth0 prison
Kubernetes has been successful for a number of reasons, not the least of which is that it takes care of things that application developers may not want to bother with – such as, for example, networking. Multus is a feature that can be used on top of Kubernetes to enable complex networking use cases.