Sponsored Post
Capturing Network Traffic anytime
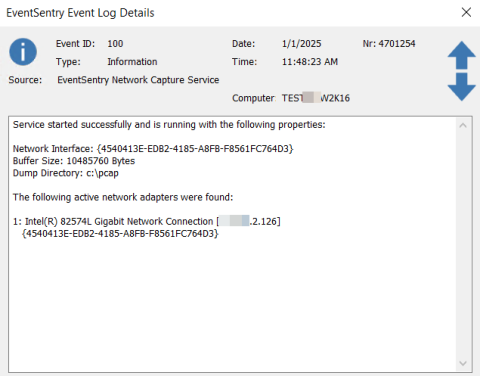
Capturing network traffic is usually done either for security reasons or to troubleshoot networking issues. But by the time you initiate a network capture (either manually or automatically) it’s often too late already – the train has already left the station. Point in case: Say your SIEM (obviously EventSentry) detects abnormal or suspicious behavior in a log and a network capture is initiated.