Operations | Monitoring | ITSM | DevOps | Cloud
The latest News and Information on CyberSecurity for Applications, Services and Infrastructure, and related technologies.
Detection rules for SIGRed vulnerability
On July 14, 2020, Microsoft released a security update related to a remote code execution (RCE) and denial of service (DoS) vulnerability (CVE-2020-1350) in Windows DNS Server (2003 - 2019).
Detect Content Security Policy (CSP) violations with Raygun
Deliver CASB policy alerts via OnPage to ensure rapid response
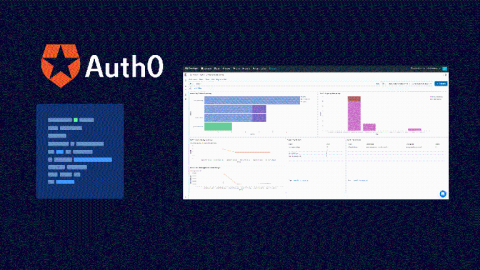
Unleash your Auth0 Log Insights With Coralogix
Auth0 is one of the top leading identity management platforms in the world. It’s focused on providing solutions for application builders, specifically solutions needed for custom-built applications. Auth0 provides expertise to scale and protect identities in any application, for any audience. This post will show you how Coralogix can provide analytics and insights for your Auth0 log data – including performance and security insights.
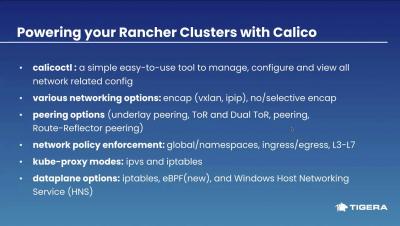
How to scale your Rancher cluster by choosing the right networking options
Guard Your Business Like a Warrior with These 10 Tools
Cybersecurity has been a core issue in business management and growth. As businesses try to manage more remote teams, it’s important now more than ever. With technology becoming an integral part of our everyday lives, we’re exposed to an ever-growing risk of cyber-attacks and malicious technological crimes. According to a recent study, on average, hack attacks occur every 39 seconds. That is, one in three Americans is a victim of cybercrime every year.
CI/CD Detection Engineering: Splunk's Security Content, Part 1
It's been a while since I've had the opportunity to take a break, come up for air, and write a blog for some of the amazing work the Splunk Threat Research team has done. We have kept busy by shipping new detections under security-content (via Splunk ES Content Update and our API). Also, we have improved the Attack Range project to allow us to test detections described as test unit files.
Nation-State Espionage Targeting COVID-19 Vaccine Development Firms - The Actions Security Teams Need To Take Now!
Throughout the duration of COVID-19, there have been consistent rumors of increased nation-state espionage. In parallel, many recent ransomware strains have a COVID-19 tie-in. Now the United Kingdom's National Cyber Security Centre (NCSC), published an advisory report that the threat group APT29 is targeting governmental, diplomatic, think-tank, healthcare and energy targets for intelligence gain which are involved in COVID-19 vaccines development and testing.
The LLMNR/NBT-NS strike
Link-Local Multicast Name Resolution (LLMNR) and NetBIOS Name Service (NBT-NS) are two protocols that are used to identify a host address on a network when the DNS name resolution, which is the conventional method, fails to do so. When a DNS server is unable to resolve a request from a requester machine, the latter broadcasts a message to its peer computers asking for the location of the required server. Hackers leverage this operation to steal the credentials of the requester machine.