Operations | Monitoring | ITSM | DevOps | Cloud
The latest News and Information on CyberSecurity for Applications, Services and Infrastructure, and related technologies.
Early Ransomware Detection and Response
Data Security and Privacy Techniques for Everyone
Extending security and governance with Sysdig and IBM Cloud Pak for Multicloud Management
Survey: Remote Work Leads to Increase in Security Issues
Over the past several months, the world has changed as we know it. The COVID-19 pandemic has transformed the way many companies do business, with more virtual events, video calls, and curbside pickups than ever before. Although challenging at times—we miss attending live events and other social activities—this pandemic has forced many companies to think outside of the box. The traditional ways of doing business were no longer feasible or even legal in some cases.
I Can See Securely Now
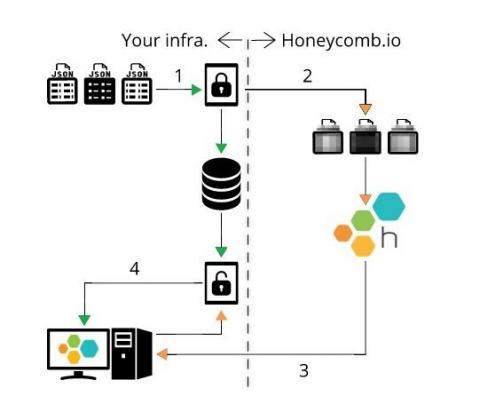
Pretty much every organization of any size is paying close attention to the adoption of security practices in order to manage and protect their most sensitive data, including personal identifiable information (PII), personal health information (PHI), or other customer and financial data. For any team using SaaS tools, data protection is a table-stakes requirement. For compliance regulated industries — banking, financial services, healthcare.
Integrate your IDS + monitoring with the Sensu Tripwire asset
Tripwire, created by our friend Gene Kim, is a popular intrusion detection system (IDS) with both commercial and open source offerings. As a fun side project, I put together a Tripwire asset for Sensu. While this is more a prototype than anything else, I wanted to take this opportunity to offer some background on IDS, Tripwire, and integrating intrusion detection into your monitoring workflow, with the overall aim of illustrating how easy it is to deploy solutions with Sensu.
Orchestration and Automation Helps Defense, Intelligence Personnel Tackle Higher-Level Tasks
What if you could get your hands on a force multiplier that got rid of the repetitive, routine work that was tying down your team, got more productivity out of your assembled work force, and gave everyone a more challenging, meaningful to-do list that made better use of their knowledge, experience, and passion?