Operations | Monitoring | ITSM | DevOps | Cloud
How to be a successful project owner (without micromanaging)
Connecting the dots for security analysts
Purchase Management-Driven Transformation: Efficient ITAM Begins Here
Growth is generally considered to be a healthy characteristic of a business. But, if the firm cannot establish systems that can take care of that growth, it might end up digging a hole for its operations.
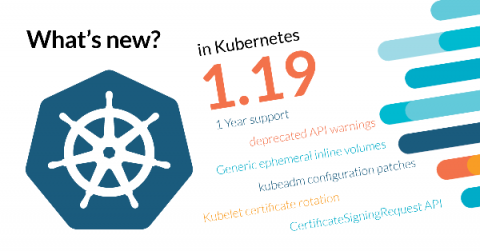
What's new in Kubernetes 1.19?
Kubernetes as a project is maturing, support has been increased from nine to 12 months, and there’s a new protocol in place to ensure a steady progress on feature development. Also, many of its new features are meant to improve the quality of life of its users, like Generic ephemeral inline volumes, or the structured logging.
How to Secure the network of your GKE Cluster
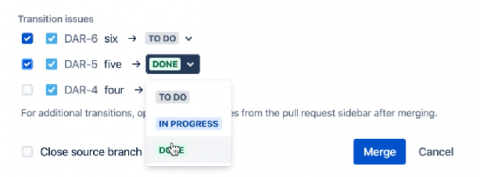
Transition Jira issues on merge
Turn Mattermost into a shared CLI with custom integrations
Nimbella and Mattermost today announced that they are offering a solution that allows any enterprise using Mattermost to easily build and run custom slash commands and apps with enterprise security capabilities.
Protecting Patient Data Through Strict Access Rights Management
Ivanti Neurons Workspace: Deliver Faster Resolutions Without Disrupting Your Customers
When was the last time an IT conversation reminded you of the movie “Casablanca”? That happened to me recently when I was talking with another IT professional about Ivanti Neurons. We discussed how Ivanti Neurons will make life easier for IT by delivering more self-servicing, self-healing and self-securing experiences.