Operations | Monitoring | ITSM | DevOps | Cloud
Introducing the o11yday Bootcamp
Getting started with observability (o11y) is now easier than ever with the new step-by-step o11yday Bootcamp guide. Now’s a great time to try out Honeycomb, get help if you’re stuck, and pick up a few holiday presents along the way.
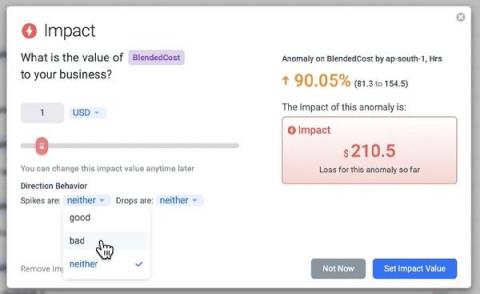
Introducing: Business Impact Alerts
Anodot is the only monitoring solution built from the ground up to find and fix key business incidents, as they’re happening. As opposed to most monitoring solutions, which focus on machine and system data to track performance, Anodot also monitors the more volatile and less predictable business metrics that directly impact your company’s bottom line. Now there’s an easy way to measure the business impact of every incident.
How Active Directory Management Tools Help Quickly Find and Troubleshoot Issues
Active Directory is part of Microsoft Windows software environments primarily for networks where some sort of domain control is required. The service is much more than just authenticating and authoring access to network resources. Active Directory is also used to enforce various network security policies, enable various processes, and enable various services. Active Directory consists of a logical structure that allows the server to execute the appropriate actions, authentication, services, and so on.
Best practices for monitoring authentication logs
If you are running a user-facing web application, you likely implement some form of authentication flow to allow users to log in securely. You may even use multiple systems and methods for different purposes or separate groups of users. For example, employees might use OAuth-based authentication managed by a company-provided Google account to log in to internal services while customers can use a username and password system or their own Google credentials.
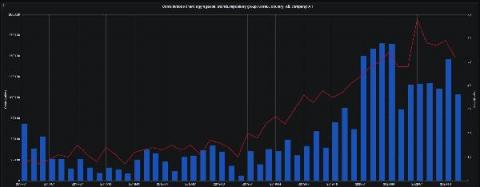
Synthetic Monitoring: When Bad things Happen to Good Checks
Running synthetic monitoring thinking it will match up with a user’s reality throw for throw is a fool’s game. While you can test in prod, your testing parameters are limited by an insider’s knowledge of the transaction’s pathways – making true objectivity challenging to achieve in testing. Yet still, every transaction tells a story.
Cortex 2020 year in review
2020 is coming to an end, and we can definitely say it was an amazing year for Cortex. Dare I say, it has been the best year so far! It was a year filled with huge milestones for the project. We released the first major version 1.0.0 back in April, along with introducing some versioning rules to avoid breaking changes to our users.
5 Takeaways from Gartner's 2020 IOCS Conference
I recently had the pleasure of attending the Gartner IT Infrastructure, Operations & Cloud Strategies (IOCS) Conference. Like most events in 2020, this event was virtual and brought together infrastructure and operations (I&O) leaders from across the world together to redefine, reassess, and prepare for what normal might be in the near future. Here are some of the major takeaways from my experience at this four-day event.
2020 Recap from a CTO's Perspective
Like pretty much every company in 2020, Civo has had to deal with some unexpected world events! To wrap up the year, I thought I'd put together some of the most significant developments in our company from a CTO's perspective, and how they will affect us looking forward into the next year.
Detect CVE-2020-8554 using Falco
CVE-2020-8554 is a vulnerability that particularly affects multi-tenant Kubernetes clusters. If a potential attacker can create or edit services and pods, then they may be able to intercept traffic from other pods or nodes in the cluster. An attacker that is able to create a ClusterIP service and set the spec.externalIPs field can intercept traffic to that IP. In addition, an attacker that can patch the status of a LoadBalancer service can set the status.loadBalancer.ingress.ip to similar effect.