Operations | Monitoring | ITSM | DevOps | Cloud
Tutorial: Advanced mobile alerting for AzureSentinel with SIGNL4
Trouble Ticketing is Dead. Long Live Collaborative Ticketing!
Ticketing systems have remained largely unchanged for three decades. Teams supporting either legacy or DevOps applications both suffer high costs.
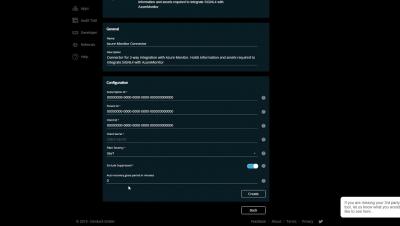
December 2019 Update: User roles, App enhancements and Azure Sentinel integration
Our December update includes a new role model for users in a SIGNL4 team, great new app features and integration with Azure Sentinel. Two default user roles are now available in each SIGNL4 team: Administrator and User. This allows for restricting standard user rights versus administrative access. For existing teams, all users are migrated to administrators, i.e. you should check this role assignment and downgrade some team members to users yourself if necessary.
What is Statuspage?
Five Ways How OnPage Reduces Physician Burnout
Physicians surveyed listed administrative tasks as a key cause of frustration and physician burnout. Accordingly, this results in workplace issues including, delays in communication, mishaps in surgery and monitoring failures. Fortunately, OnPage curated its HIPAA-compliant, clinical communications solution to help reduce physician burnout and improve care team collaboration, preventing dire consequences in the process.
Best practices for managing alerts with Slack and Opsgenie
When Opsgenie and Slack team up, incident management is smoother and more intuitive. With this powerful integration, users are enabled to rapidly respond to and resolve alerts directly from Slack, using buttons or /genie commands to mute notifications, get alert details, view on-call schedules, and much more. Here are some best practices to help teams avoid alert fatigue but always stay informed.
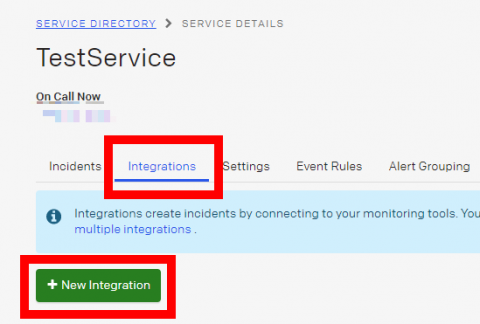
Sending monitoring notifications to your PagerDuty
Here are short instructions how to integrate your AppBeat Monitoring with PagerDuty.
How CSPs Can Drive Digital Transformation & 5G Success with Automation
Light Reading’s Phil Harvey recently sat down with Resolve’s Larry Lien at Network Virtualization and SDN Americas to explore how communication service providers (CSPs) are benefitting from automation, what types of processes can be automated, how to successfully navigate the automation journey, and how Automation Centers of Excellence can accelerate digital transformation.
Storing and enriching alerts for information security with Elasticsearch
Within Elastic, the information security team is tasked with security detection and analytics, among many other activities of a typical information security team. To find abnormal and malicious behavior within our environment we leverage Elastic SIEM for investigations and threat hunting. When we find a pattern of behavior we want to be alerted on during an investigation or hunt we take the request JSON behind our investigation and put in to Watcher for alerting.