Operations | Monitoring | ITSM | DevOps | Cloud
Tips on making on-call manageable
On-call responsibilities are a crucial part of many industries, ensuring that businesses can provide round-the-clock support to their customers. However, the demanding nature of on-call duty can lead to burnout and reduced productivity if not managed effectively. In this article, we will explore various strategies and tips to make on-call more manageable, enabling professionals to maintain a healthy work-life balance and deliver exceptional service.
How Schneider Electric reduced MTTI and alert noise by consolidating monitoring tools
The Art of Alert Management
With the ever-growing landscape of digital technology and the internet of things (IoT), businesses are becoming increasingly reliant on complex systems to monitor and manage their operations. This dependency has resulted in an explosion of alerts and notifications, overwhelming IT teams and affecting overall productivity. It’s never been more critical to have an effective alert management strategy in place to ensure the smooth running of your organization.
SIGNL4 Onboarding: Routing Alerts to Teams using Distribution Rules
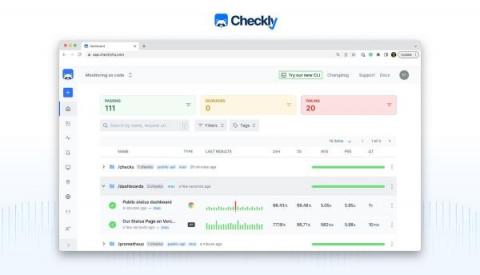
Synthetic monitoring as Code with Checkly and ilert
This post will introduce Checkly, the synthetic monitoring solution, and their monitoring as code approach. This guest post was written by Hannes Lenke, the CEO, and co-founder of Checkly. First, thanks to Birol and the ilert team for the opportunity to introduce Checkly. ilert recently announced discontinuing its uptime monitoring feature and worked with us on an integration to ensure that existing customers could migrate seamlessly. So, what is monitoring as code and Checkly?
Overlapping Maintenance Windows in Moogsoft Cloud | Moogsoft Product Videos & How-Tos
IT Incident Management - What is it and how to do it?
Are you tired of dealing with IT incidents that seem to pop up at the worst possible times? Do you find yourself struggling to keep track of all the moving pieces involved in resolving incidents? If so, it’s time to revitalize your incident management strategy. In this article, we’ll explore the key pillars of incident process management, best practices, and how technology can help streamline your process.
What makes AlertOps the top choice as an Opsgenie alternative
Alert Tuning Recommendations: Reinventing Anomaly Alerts with Anodot
In the complex and dynamic realm of data analytics, real-time anomalies serve as insights to issues a business faces. A pervasive and enduring conundrum persists: accurately discerning between anomalies of significant importance and those of lesser consequence. This distinction is a nontrivial task as not all anomalies bear the same weight.