Why You Should Migrate from Legacy Apps to IT Essentials Work
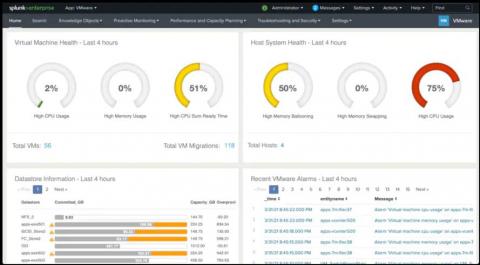
If you were using the Splunk App for Infrastructure (SAI) and / or other Splunk apps for infrastructure — *nix, Windows, and VMware — you’ve probably enjoyed the ease and quickness these apps offered to get started with basic infrastructure monitoring tasks.