Operations | Monitoring | ITSM | DevOps | Cloud
The latest News and Information on IT Networks and related technologies.
A Day in the Life of a NOC Engineer
While your regular job may allow you to make your snooze button your best friend, what would you say to a job that requires 6-8-hour shifts (probably night shifts too) and demands that you be on call 24/7? Welcome to the life of a NOC engineer.
Tech Confessions - Ancient Artifacts
Is AI a Benefit or Risk to MSPs?
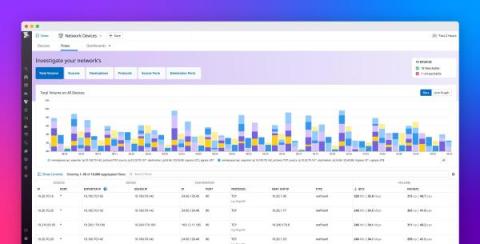
WhatsUp Gold 2023.0: Greater Transparency and Wider Access to Network Data
One of the greatest challenges for an IT team is visibility. How can you prove the value of your IT team’s accomplishments when no one can see what – or how well – you’re doing? Progress WhatsUp Gold release 2023.0, available as of June 21, 2023, is set to change that. This release includes several exciting updates meant to provide better data access to all.
What's Your Flow? The Differences Between J-Flow, NetFlow and More
To track IP traffic flows and record metadata, IT professionals use network flow monitoring protocols and supporting solutions to collect and analyze data.
Monitor network access with Twingate's offering in the Datadog Marketplace
Twingate is a network access platform that enables customers to deploy a zero trust authentication layer with their infrastructure as code (IAC) provider of choice. Using this model, you can program strict access control rules that can be updated and co-deployed alongside changes to your infrastructure. Each time a user establishes or closes a connection to a resource, Twingate documents the event with details such as the port, the volume of data transferred, and user identification.
Monitor NetFlow traffic data with Datadog
NetFlow is a network protocol that enables devices to report key traffic flow data such as origin, direction, and overall volume.
Understanding Network Traffic Monitoring
Network traffic monitoring has become critical in today's digital age, where businesses rely on various applications and services to operate. As the amount of data transmitted over networks continues to grow exponentially, network administrators must keep a close eye on the traffic to ensure optimal network performance and security. Network administrators must have a deep understanding of packet flows, collection methods, and analytics to ensure that their networks are secure and performing optimally.
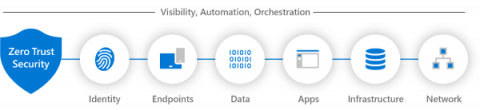
Applying Zero Trust to Data Centre Networks
Zero trust isn’t an approach that can be delivered by buying a single product that claims to provide it. Instead, it is an approach that needs to be understood and implemented in complementary ways across an organization’s IT systems. We recently hosted a webinar titled Applying Zero Trust to Data Centre Networks to provide guidance on how organizations can use zero trust to enhance the security of their IT systems. The webinar details are below, after a summary of the topics covered.