Operations | Monitoring | ITSM | DevOps | Cloud
The latest News and Information on CyberSecurity for Applications, Services and Infrastructure, and related technologies.
6 Things You Should Know Before Incorporating Data Into Your Business Plan
Cilium network policy security tutorial on Civo
Achieve End-to-End Network Visibility for SASE
Using OpenID Connect identity tokens to authenticate jobs with cloud providers
Introducing OpenID Connect identity tokens in CircleCI jobs! This token enables your CircleCI jobs to authenticate with cloud providers that support OpenID Connect like AWS, Google Cloud Platform, and Vault. In this blog post, we’ll introduce you to OpenID Connect, explain its usefulness in a CI/CD system, and show how it can be used to authenticate with AWS, letting your CircleCI job securely interact with your AWS account, without any static credentials.
Data-Aware Security: How to Take a 360 View of Cloud Security
Don’t let your organization fall victim to data exposure; a well-defined strategy will cover all aspects of the cloud shared responsibility model and keep your data secure. Not long ago, security concerns were the number one reason IT executives hesitated to move workloads to the cloud. Much has changed since then. Security is now considered one of the great strengths of both cloud infrastructure and software-as-a-service (SaaS) platforms. But that doesn’t mean total security is assured.
Heroku Vs. AWS: Data Security Comparison
What is the Most Vulnerable Data My Company Holds?
Data security is on every priority list in 2022. With the frequency of breaches never higher, many businesses assess their situation and ask cybersecurity questions. With cybersecurity policy, everything boils down to risk. Ultimately, every decision-maker wants to know, “how likely are we to be attacked?” Many believe cybercriminals only target certain kinds of data. Sensitive information, high-value financial data, and medical records are all widely accepted to carry a high risk.
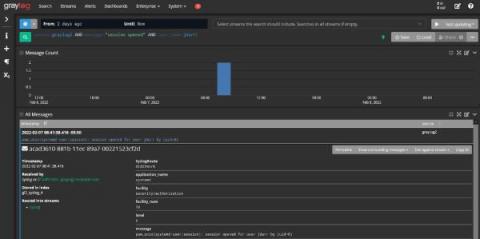
Using Log Management as a Security Analytics Platform
With the rising tide of data breach awareness, your senior leadership is asking you to mitigate cybersecurity risk with security analytics. You’ve built up the use cases and started researching different platforms. Then, you realized: you’re not sure you have the budget. The typical security analytics platforms come with upfront technology costs as well as the “hidden fees” associated with training your team members. You know you need to use analytics to help mitigate risk.
A practical guide to container networking
An important part of any Kubernetes cluster is the underlying containers. Containers are the workloads that your business relies on, what your customers engage with, and what shapes your networking infrastructure. Long story short, containers are arguably the soul of any containerized environment. One of the most popular open-source container orchestration systems, Kubernetes, has a modular architecture.