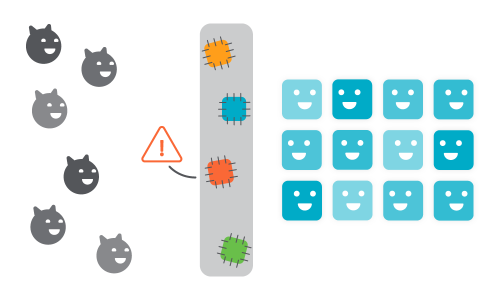
Making a Big GDPR CCPA Issue a Small One
British Airways, now there is a big GDPR issue. 500,000 people were affected over 15 days. Reputation damaged, untold revenue lost and a $230 million dollar fine and that is before any damages are paid. In my former life, I thought GDPR was a boring tick box exercise, it really could not be further from the truth. It is a scare your pants off ride, one that needs to be taken very, very seriously. Your company’s existence is at stake.