Operations | Monitoring | ITSM | DevOps | Cloud
The latest News and Information on CyberSecurity for Applications, Services and Infrastructure, and related technologies.
How Orange Business Services is building a better SIEM with Elastic
I’m a security analyst at Orange Business Services in Paris, and one of my current projects for the Orange Group is implementing a new SIEM based on the Elastic Stack. In this blog post, I’ll share why we chose Elastic and how we were able to integrate Elastic into our existing SIEM, resulting in faster investigations and saving our engineers’ time. So follow along.
Log Analytics and SIEM for Enterprise Security Operations and Threat Hunting
IT analytics in 90 seconds: Stay on top of every threat to your endpoints
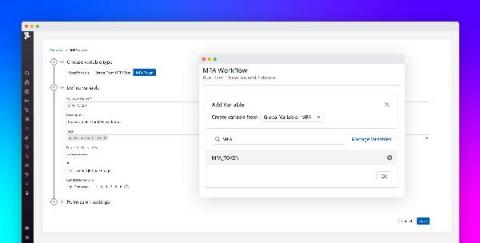
Introducing multi-factor authentication in Datadog Synthetic tests
Multi-factor authentication (MFA) is an increasingly popular method for securing user accounts that requires users to provide two or more pieces of identifying information when logging into an application. This information can consist of unique verification links or codes sent to the user’s phone or email address, as well as time-based one-time passwords (TOTPs) generated by authenticator applications or hardware.
Webinar featuring IDC's Mark Leary: Make your IT operations future-proof with the Branch of One architecture
At the start of the pandemic, IT organizations had to undergo radical changes to support remote work. Given the urgency to shift to remote operations, IT admins opted for band-aid solutions to retain business continuity and stay connected to the core of their networks from remote locations. But now, many organizations are moving toward hybrid workforce options with employees choosing to work from both their home and office locations.
Deep-dive into Open Policy Agent + Conftest + GateKeeper - Shimon Tolts & Noaa Barki
Not Another Phishing and Ransomware Blog!
What can I say further about Ivanti’s mobile threat defense (MTD) solution for iOS, iPadOS and Android devices that has not already been mentioned in any of my previous blogs and quick video demos? If I was to state where Ivanti has a clear advantage over other unified endpoint management competitors, it is with Ivanti’s MTD solution.
Our Workflow for Security Releases using GitHub Security Advisories
We recently started using GitHub Security Advisories as part of our workflow for pushing out security releases. This post will give a brief introduction on how they work, how we use them, some of their limitations, and how we overcome them. We are still experimenting with this workflow, but the information could still be helpful for some while others might have suggestions how we could do things better.
Detecting Trickbot with Splunk
The Splunk Threat Research Team has assessed several samples of Trickbot, a popular crimeware carrier that allows malicious actors to deliver multiple types of payloads.