Managing Microsoft 365? See What You're Missing
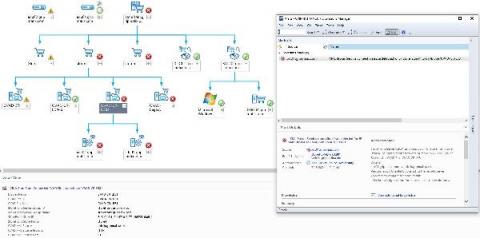
If a customer has an issue with any part of Microsoft 365, MSPs just don’t have the native visibility to identify the root cause, let alone respond to and remediate the problem. Most of the time, it’s little more than checking Microsoft’s Service Health status to see if Microsoft knows it’s having a problem.