Operations | Monitoring | ITSM | DevOps | Cloud
Today's Big Leap for Tomorrow
How Government Agencies Defend Against Increasing Cyberthreats
Whether military, a civilian agency, or even a public education institution, organizations across the public sector have witnessed a substantial increase in cyberattacks. There were a number of hits on education around this time last year, and then on health-related agencies as the COVID-19 pandemic struck. So, how do government agencies ensure their security posture is up to the task of defending against increasingly opportunistic forces of evil?
Webpagetest Joins Forces with Catchpoint
I’m incredibly excited about the future of Webpagetest and web performance testing in general with today’s announcement that Webpagetest and Catchpoint will be joining forces and I hope you’re as excited as I am for the possibilities it will bring.
Let's Talk AIOps: Part 2: Things to Think About & the PagerDuty Approach
This is the second in a two-part blog series about AIOps where I sit down with Julian Dunn, Director of Product Marketing at PagerDuty, to level-set on the hot DevOps topic. The first post discussed whether AIOps was just marketing fluff and whether ITOps actually has an AIOps problem. Let’s continue…
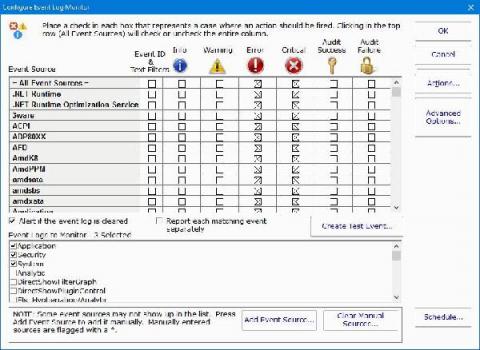
Windows Server Monitoring with Pandora FMS
Pandora FMS is a proactive, advanced, flexible and easy-to-configure monitoring tool tailored to business itself. It adapts to all needs both in servers, network computers, devices and whatever is necessary. In this article, we will focus on Windows Server monitoring, using the software agent installed on our server.
Monitoring Java applications with Elastic: Multiservice traces and correlated logs
In this two-part blog post, we’ll use Elastic Observability to monitor a sample Java application. In the first blog post, we started by looking at how Elastic Observability monitors Java applications. We built and instrumented a sample Java Spring application composed of a data-access microservice supported by a MySQL backend. In this part, we’ll use Java ECS logging and APM log correlation to link transactions with their logs.
Hey - a Thoughtful Email Reinvention Tool from Basecamp
Email communication has been around for almost as long as the Internet. But although it continues to be of the best ways to provide a personal and direct conversation, it’s also a source of pain for many. Our inboxes have become an untidy clutter of messages, where most emails either are irrelevant or spam. Prominent email service providers such as Google have done a lot to improve the experience over time.
September 2020 Update: All-new Webhook and API Key Management
Our September update provides you with self-service API key management from the SIGNL4 web portal. Finally, you can fully exploit our comprehensive REST API. We also improved management of outbound webhook which can update your systems with any information on Signl handling. It is now possible to manage API keys for the SIGNL4 API in the SIGNL4 account portal. Click on the “Developer” menu item to manage API keys. Keys issued here can then be used to call SIGNL4 REST API functions.
How to Implement a Strong COVID-19 Cybersecurity Plan
As COVID-19 forces more employees to work from home, companies are reevaluating their cybersecurity plans to place an increased emphasis on securing remote access, as well as phishing and ransomware prevention. Here are some of the most important security basics to include in your COVID-19 cybersecurity plan.